About memy stats
Information About me
I'm a pro-active and ambitions person, curious and eager to learn anything. Ex-colleagues describe me as a jack of all trades, nice to work with and pragmatic.
BSc.
Computing Science
Radboud University
MSc.
Cyber Security
Radboud University
15+
Projects
Completed
10
Years Active
In Cryptography
My Skills
My Timeline
2026-PRESENT
Self-Employed Cryptographer - MvL Technologies
Helping organisations in their migration towards quantum-safe cryptography, through the offering of consultancy and self-developed tooling.
2021-2025
Scientist Integrator and Portfolio Manager - TNO
Worked in the Unit ICT, Strategy & Policy, in the department Applied Cryptography and Quantum Algorithms. As a scientist integrator, I took on various activities that typically belong to the role of consultant, project lead and scientist, such that I was involved in translating the client's problem to a solution, working out requirements and an architecture for that solution and implementing it. As portfolio manager of Quantum Safe Technologies, I was responsible for the development and execution of the roadmap, strategy and vision for this topic. This included bringing experts, consultants, business developers and (higher) management together and agreeing on a systematic approach.
I also coordinated the internships within our department and set up collaborations with other departments within TNO.
I co-organised the PQC Symposium 2024 and published an article in 2024 IEEE International Conference on Big Data.
2019-2021
MSc. Cyber Security - Radboud University
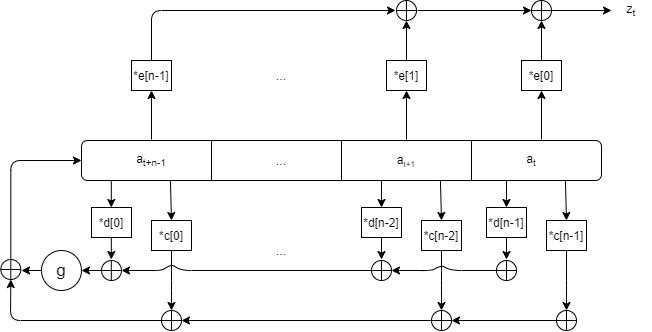
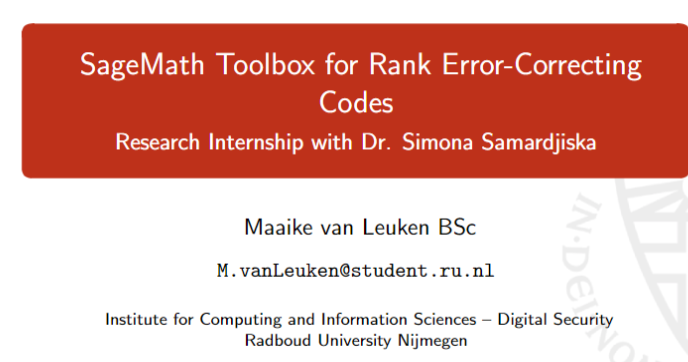
My main focus was on cryptography. During my research internship under supervision of Dr. S. Samardjiska, I added rank-based cryptography to the SageMath toolbox. I conducted my thesis under supervision of Prof. J. Daemen, "runaway generators and their security and efficiency".
2016 - 2019
BSc. Computer Science - Radboud University
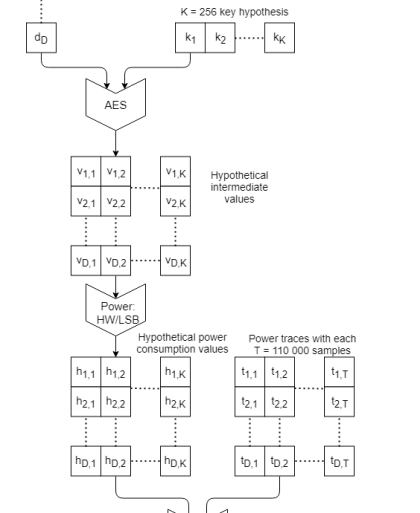
Followed the Cyber Security track. Conducted my thesis under supervision of Prof. L. Batina, "Comparing Correlation Coefficient and Difference of Means in a Differential Power Analysis Attack".
2015-2017
Propedeuse Physics - Radboud University
Completed courses on linear algebra, calculus, classical mechanics and thermodynamics.
Quantum SafetySecurity
Fixing your Cryptography
Compliancy
To EU/Dutch Legislation
and Industry Standards
Crypto-Agility
To swiftly and efficiently
upgrade cryptography
PQC Migration
Protecting assets against
the quantum threat
Through Independent Advice, Research and Tooling
Cryptographic Governance & Compliance
Organisations increasingly need to demonstrate cryptographic control to regulators, auditors, and customers. I assist with defining policies, governance structures, and technical controls aligned with frameworks such as post-quantum migration guidance, industry standards, and security best practices. This ensures that cryptography is not only implemented correctly, but also managed as a strategic security capability.Cryptographic Agility
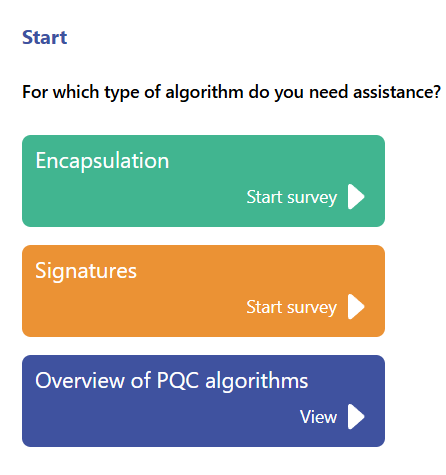
Future-proof systems must be able to evolve cryptography without requiring large-scale redesigns. This aids in protecting against any cryptographic weaknesses, including quantum vulnerabilies. I help design architectures and processes that allow cryptographic algorithms, key sizes, and trust anchors to be updated safely and efficiently. This includes abstraction patterns, key lifecycle management strategies, and governance models that enable rapid response to emerging vulnerabilities or regulatory requirements.Post-Quantum Cryptographic Migration
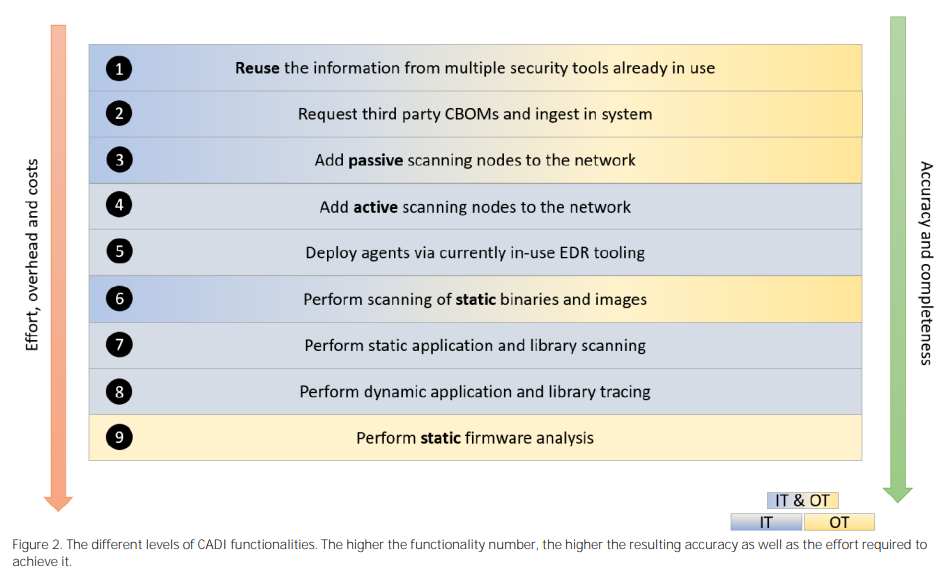
Many systems still rely on legacy or soon-to-be-deprecated algorithms. I support organisations in designing and executing structured migration strategies toward modern and quantum-resistant cryptography. This includes prioritising high-risk assets, assessing migration effort, designing transition architectures, and minimising operational disruption during the transition.Identifying Cryptographic Assets
Through the omni-presence of cryptography, it is easy to lose track of where cryptography is used across systems. I help identify cryptographic assets through providing my own tooling, or advising on which other tooling to use. The result is a structured inventory of cryptographic dependencies connected to business processes, that forms the foundation for risk assessment, governance, and migration planning.
Assessing Migration Effort
Once cryptographic assets are identified, the next step is understanding where to migrate to and how difficult this migration is. I assess the technical and operational complexity of cryptographic migration across systems, including software dependencies, hardware constraints, protocol compatibility, and key management processes. This allows organisations to prioritise migrations based on risk, effort, and business impact.
Migration Planning
Effective cryptographic migration requires careful planning to avoid operational risk and ensure continuity. I design structured migration strategies that define timelines, architectural changes, and transition mechanisms such as hybrid cryptography or phased deployments. The goal is to enable a controlled transition toward modern and post-quantum cryptographic standards while maintaining security and business continuity.
My PortfolioMy Work
Here is some of my publicly available work.
My ThoughtsMy Blogs

Cyberaanval voorkomen? Formele hardware verificatie cruciaal
1 oktober 2024
Een zelfrijdende auto die op afstand bestuurd wordt door een aanvaller. Gamecontrollers waarmee je het betalen van spelletjes kunt omzeilen. Of mensen die machines van grote techbedrijven namaken. Allemaal voorbeelden waarbij de hardware niet veilig genoeg in elkaar zat, waardoor mensen er misbruik van maakten. Om dit soort fouten te voorkomen, moeten we de cryptografie in hardware controleren en beveiligen. En het liefst al vóórdat het gemaakt is. Dat is waar TNO aan werkt.

TNO’s view of 2030: Digital privacy and security for everyone
21 April 2023
Privacy and cyber security are the cornerstones of our digital society. ‘Digital privacy and security for everyone’ is therefore one of TNO’s ambitious goals. In 10 years, we’ll ensure that everyone can exchange data online with complete peace of mind. Together with our partners, we are making this possible with smart innovations in data encryption, quantum-safe data sharing, and secure digital infrastructure.
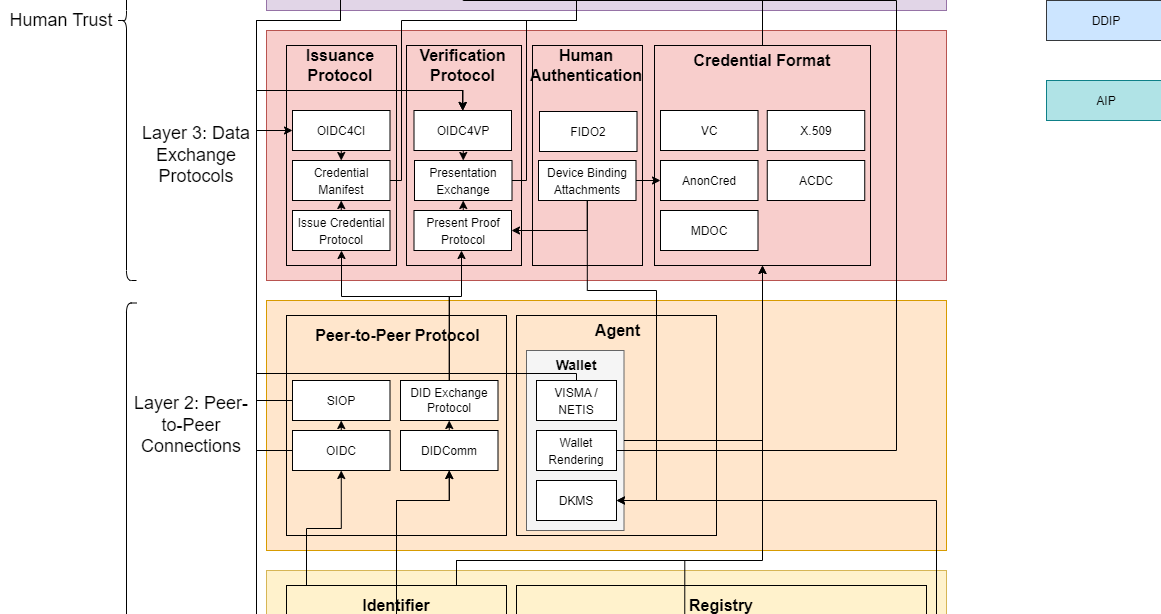
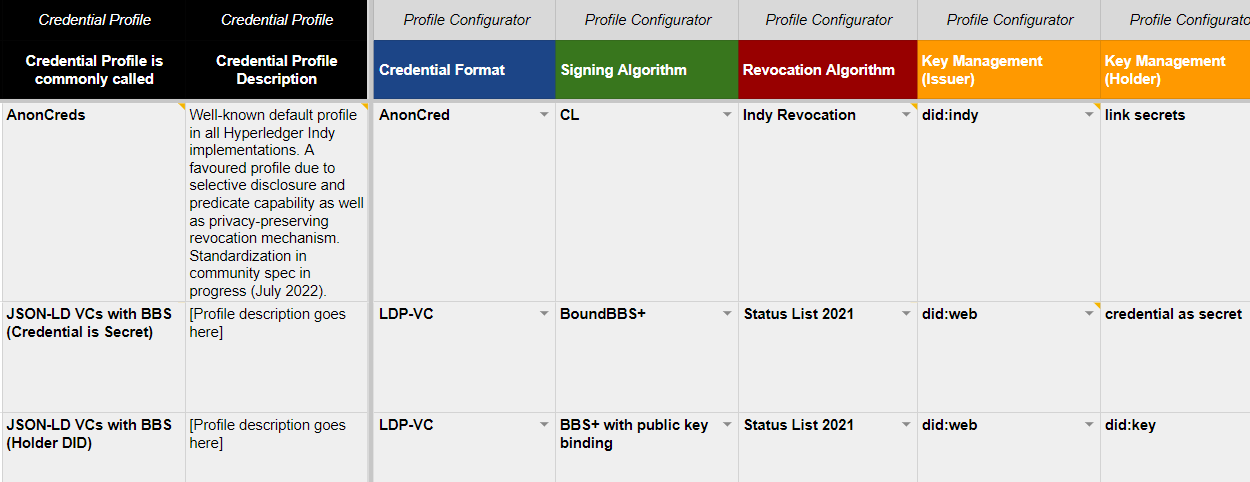
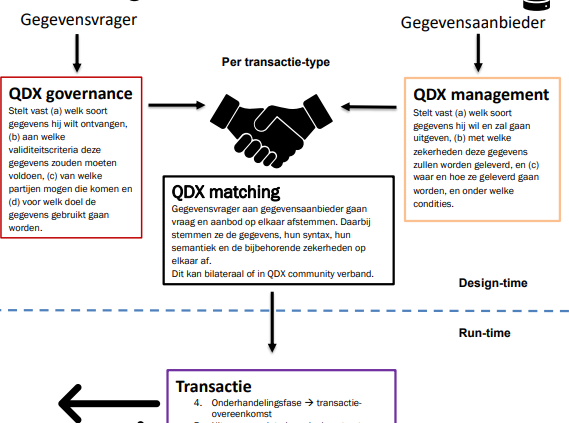
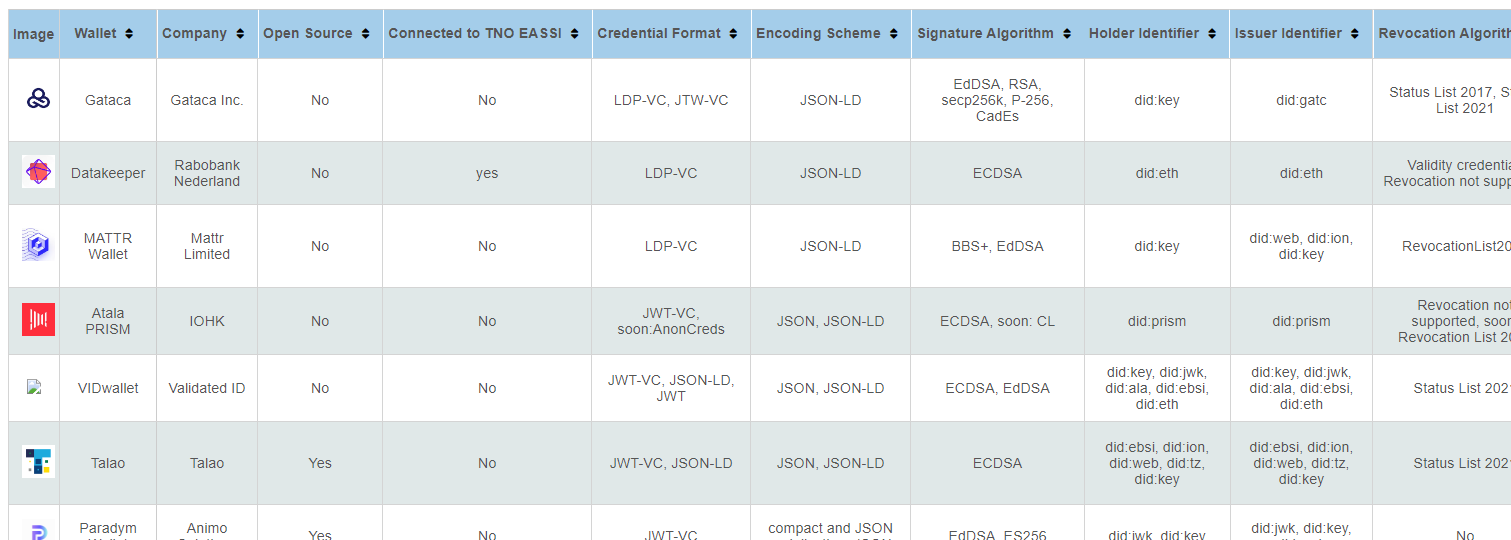
What are those SSI standards?
9 May 2023
It can be difficult for SSI adopters to figure out which standards in the context of SSI are relevant and how they relate to other standards. Our standardisation overview helps with this, by giving insight in the positioning of standards in the context of SSI.

Solving the effort of offering support for a great variety of wallets
25 November 2022
Due to competing technological approaches, there is fragmentation within the SSI ecosystem. Read our solution to this problem: TNO EASSI.